WHAT YOU GIVE, THEY GET!
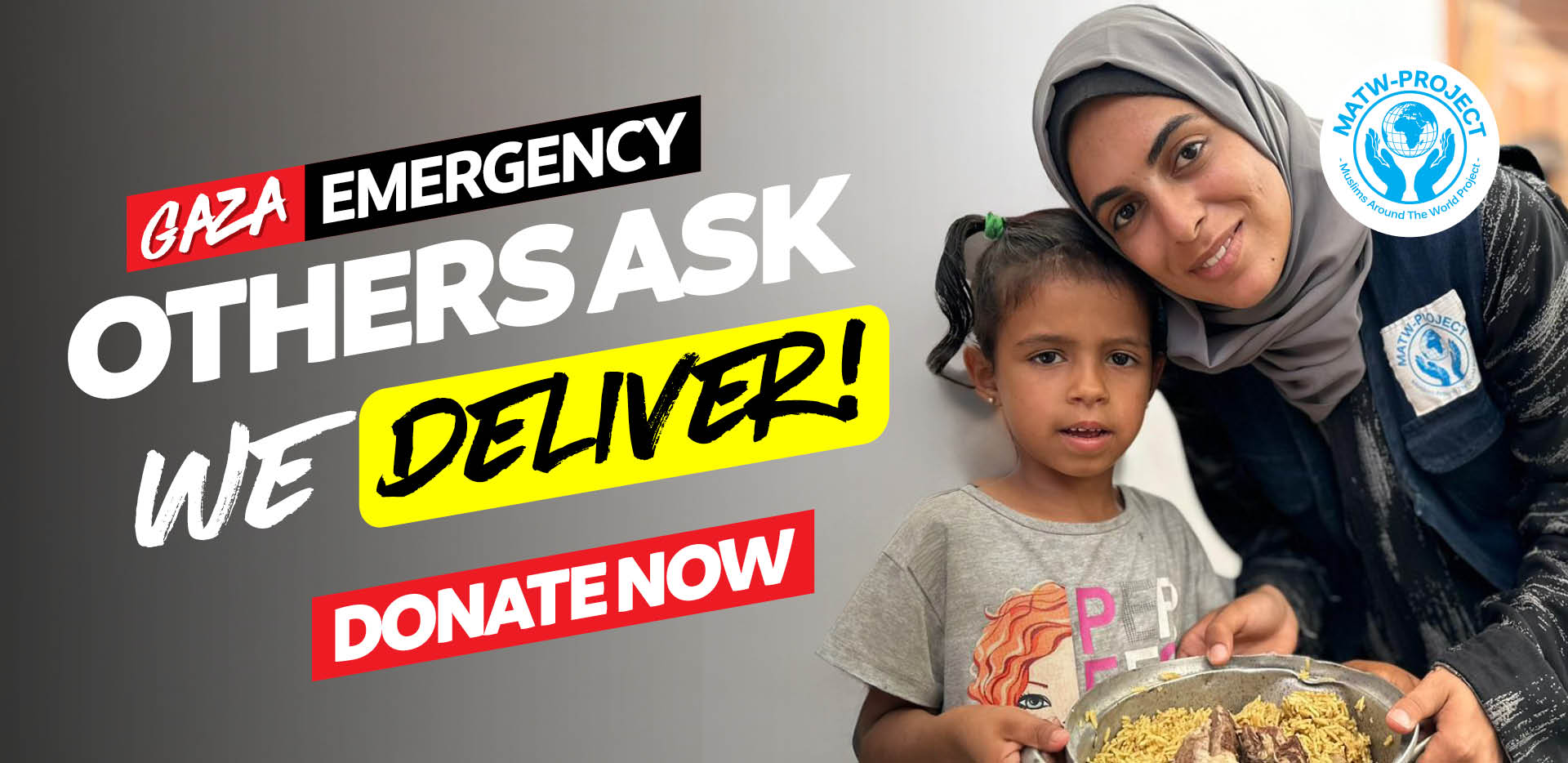
The fragile calm in Gaza has shattered. A sudden escalation in conflict has destroyed any hope of rebuilding. Our brothers and sisters in Gaza remain displaced – their homes in rubble. Living in fear, families are without food, water, medicine or shelter. Hopes for peace have been broken—yet the need for action has never been greater. MATW Project is still delivering life-saving relief. Despite the incursion, our teams are working tirelessly to support our brothers and sisters in Gaza. We’re on the ground delivering emergency shelter, food, water, medical supplies and more.

 AUD
AUD
 GBP
GBP
 EUR
EUR
 CAD
CAD
 SGD
SGD
 MYR
MYR