Start, grow, and optimize your e-commerce business seamlessly in the GCC and emerging markets.
Connect your e-commerce site with ease using preferred methods.
Share your needs or explore our Winning Products Catalog.
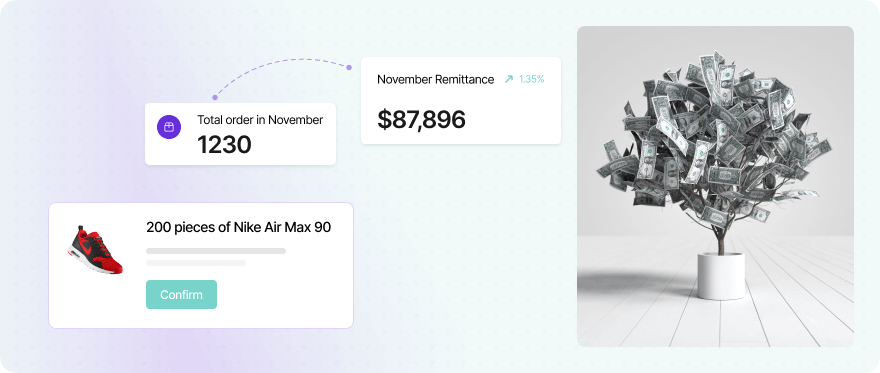
Receive your invoice weekly and collect your profits effortlessly.
Use the built-in security features in your browser to identify saved passwords that have been exposed [3]. 3. Immediate Defense Steps
This subject line typically refers to —large collections of leaked email and password pairs often traded in cybercrime forums for credential stuffing or account takeover attacks. Download 179K COMBOLIST FRESH Mail Access txt
Instead of downloading raw lists, use secure, legitimate databases to see if your own credentials have been compromised: Use the built-in security features in your browser
Turn on Multi-Factor Authentication everywhere. Even if a hacker has your "mail access" password, they cannot enter without the secondary code [9]. be aware of the following:
If you have encountered a link with this title, be aware of the following: