Arch Pro is a precision-tuned LOG to REC709 LUT system built specifically for the Pocket Cinema Camera 4K, 6K, and 6K Pro. The base set includes a Natural LUT along with Filmic and Vibrant character LUTs—each one uniquely matched to your camera’s sensor and LOG profile. This isn’t one-size-fits-all, it’s one-for-each, engineered for color that just works.
Want more? The Plus and Premium Bundles unlock stylized Film Looks and DaVinci Wide Gamut support for Resolve users.



Whether you’re a filmmaker, YouTuber, or weekend warrior, if you're working with Pocket 4K, 6K, or 6K Pro footage, this is the fastest way to make it shine. Arch Pro enhances highlight rolloff, improves skin tone, and just looks good.
Import Arch Pro LUTs right into your Pocket Cinema Camera to preview the colors live — great for livestreams, fast turnarounds, or video village. Burn it in if you want. Shoot LOG and tweak later if you don’t.


Create a cohesive cinematic look without obsessing over complex node trees. Whether you’re cutting a music video or a doc on a deadline, these LUTs hold their own — and still play nice with secondary grading and effects.


Arch Pro Plus adds 12 pre-built Film Looks that range from elegant monochromes to punchy stylization. Everything from a Black & White so classy it’d make Fred Astaire jump for joy to a Teal & Orange that could coax a single tear down Michael Bay’s cheek.


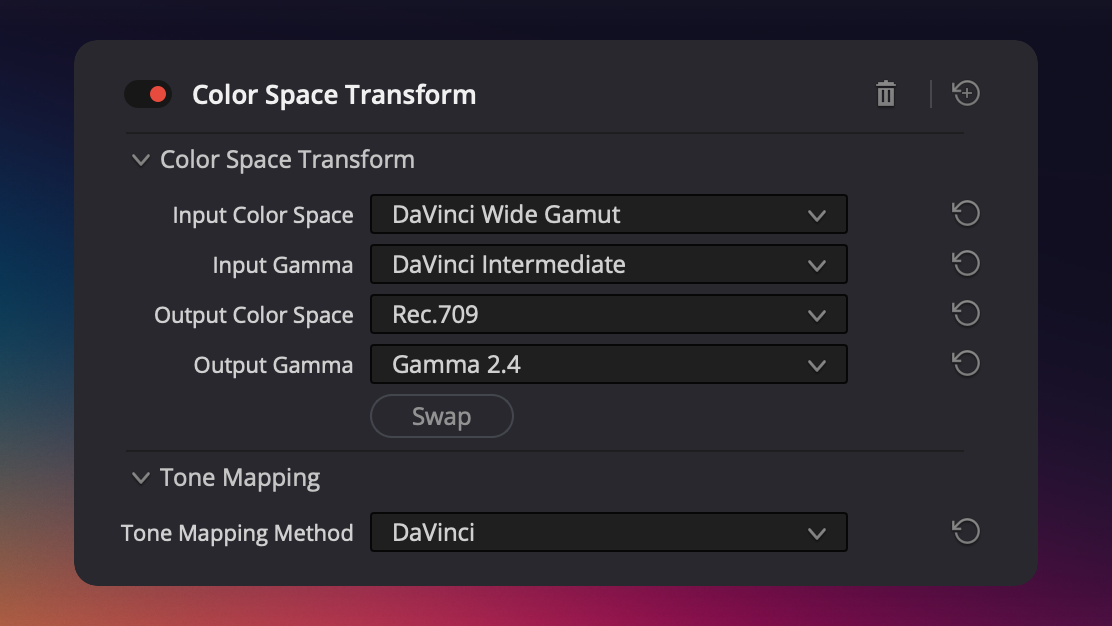
Arch Pro Premium unlocks a secret weapon: DaVinci Wide Gamut support. No Rec709 bakes. No locked-in looks. Just a clean, accurate conversion into DaVinci’s modern color space — built for real post workflows and future-proof grades.

All of these examples were shot in BRAW with Gen 5 color science. On the left: Blackmagic’s built-in Extended Video LUT. On the right: Arch Pro Natural.
This isn't showing a LOG-to-Rec709 miracle like most do, this is comparing what you’d actually get side-by-side. The difference between good enough
and being there.




























Arch Pro Plus gives you 12 distinct looks for your footage. Arch Pro Premium gives you the same looks with full DaVinci Wide Gamut support!
Use this nifty chart to help you decide which flavor of Arch Pro is right for you.
Not sure? Start with Plus — it’s what ~70% of customers choose! 24447.rar
These are just a handful of teams that rely on Arch Pro for their productions.



The top priority of this LUT is to make skin tones—of all shades—look remarkable.
Between shooting midday weddings & music festivals, I've mastered the art of the highlight roll off!
I always find myself tinting towards magenta in-camera, so I set out to fix the green channel!
Gives you a very robust starting point that holds up to heavy grading and effects.
Yanno how the Extended Video LUT just kinda looks like mud? Well, kiss that look goodbye!

Compatible with any application that supports LUTs on Windows, Mac, and iOS.
As new LUTs are developed for the set or Blackmagic Color Science evolves, you'll get updates for free!
Below is a draft essay exploring the file from a cybersecurity perspective, focusing on the risks of compressed archives and the vulnerabilities often associated with them. The Anatomy of an Archive: Analyzing 24447.rar
In the digital landscape, the file extension .rar —standing for Roshal Archive —is synonymous with efficiency, offering higher compression ratios than standard ZIP files. However, files like 24447.rar often appear in automated sandbox reports or threat intelligence feeds, serving as a reminder that compression is a double-edged sword. While it facilitates the transfer of large datasets, it also provides a convenient "wrapper" for malicious actors to hide payloads from traditional email security filters .
To handle suspicious files like 24447.rar safely, security professionals recommend using isolated environments known as sandboxes. Modern defense frameworks, such as CyberSentinel , use deep learning to analyze the "salient features" of files even when they are obfuscated. For everyday users, the rule remains simple: never extract or open a RAR file from an unverified source, as malware remains dormant until the extraction process begins.
An essay regarding a specific file like typically falls into a technical or cybersecurity context. While "24447" doesn't refer to a single globally famous document, this naming convention is common in malware analysis or data leak repositories.
The danger of a .rar file isn't always in its contents, but in the software used to open it. For example, recent vulnerabilities like CVE-2025-8088 have shown that a "path traversal" flaw in WinRAR allowed attackers to execute arbitrary code just by having a user open a maliciously crafted archive . This means that even if a user does not run an ".exe" inside 24447.rar , simply viewing the file structure could theoretically compromise a system.
Whether 24447.rar represents a legitimate data backup or a specialized malware strain, it highlights the ongoing tension between digital convenience and security. As compression technology evolves, so too must our methods for inspecting the "hidden" data within these digital containers. CVE-2024-24447 - NVD
Files such as 24447.rar are frequently used as delivery mechanisms for "infostealers" or ransomware. Because a RAR archive can contain multiple nested files, it allows attackers to bundle a malicious executable with legitimate-looking library files to evade suspicion. Furthermore, the encryption capabilities of the RAR5 format, which uses AES-256 in CBC mode , can be used to lock content so that security scanners cannot inspect the interior without a password, often provided in a phishing email.
Below is a draft essay exploring the file from a cybersecurity perspective, focusing on the risks of compressed archives and the vulnerabilities often associated with them. The Anatomy of an Archive: Analyzing 24447.rar
In the digital landscape, the file extension .rar —standing for Roshal Archive —is synonymous with efficiency, offering higher compression ratios than standard ZIP files. However, files like 24447.rar often appear in automated sandbox reports or threat intelligence feeds, serving as a reminder that compression is a double-edged sword. While it facilitates the transfer of large datasets, it also provides a convenient "wrapper" for malicious actors to hide payloads from traditional email security filters .
To handle suspicious files like 24447.rar safely, security professionals recommend using isolated environments known as sandboxes. Modern defense frameworks, such as CyberSentinel , use deep learning to analyze the "salient features" of files even when they are obfuscated. For everyday users, the rule remains simple: never extract or open a RAR file from an unverified source, as malware remains dormant until the extraction process begins.
An essay regarding a specific file like typically falls into a technical or cybersecurity context. While "24447" doesn't refer to a single globally famous document, this naming convention is common in malware analysis or data leak repositories.
The danger of a .rar file isn't always in its contents, but in the software used to open it. For example, recent vulnerabilities like CVE-2025-8088 have shown that a "path traversal" flaw in WinRAR allowed attackers to execute arbitrary code just by having a user open a maliciously crafted archive . This means that even if a user does not run an ".exe" inside 24447.rar , simply viewing the file structure could theoretically compromise a system.
Whether 24447.rar represents a legitimate data backup or a specialized malware strain, it highlights the ongoing tension between digital convenience and security. As compression technology evolves, so too must our methods for inspecting the "hidden" data within these digital containers. CVE-2024-24447 - NVD
Files such as 24447.rar are frequently used as delivery mechanisms for "infostealers" or ransomware. Because a RAR archive can contain multiple nested files, it allows attackers to bundle a malicious executable with legitimate-looking library files to evade suspicion. Furthermore, the encryption capabilities of the RAR5 format, which uses AES-256 in CBC mode , can be used to lock content so that security scanners cannot inspect the interior without a password, often provided in a phishing email.